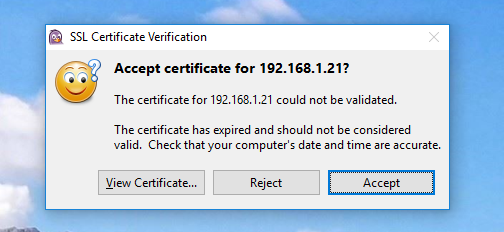
в моей работе используется локальный сервер XMPP (Wildfire, теперь называется Openfire). При использовании клиента Pidgin он всегда спрашивает меня, должен ли он принять недопустимый (истек) сертификат.
Я хотел бы, чтобы Pidgin всегда принимал его, не спрашивая меня. Как это сделать без установки нового сертификата на сервере XMPP?
Я попытался импортировать сертификат как в личное хранилище, так и в Доверенное корневое хранилище, но я все равно получаю тот же запрос. Сертификат также хранится в %APPDATA%.purplecertificatesx509tls_peers, но я все равно получаю приглашение.
вот журнал отладки при подключении:
Pidgin Debug Log : 10/4/2016 12:05:16 PM
(12:05:05) account: Connecting to account example@192.168.1.21/.
(12:05:05) connection: Connecting. gc = 04528D78
(12:05:05) dnssrv: querying SRV record for 192.168.1.21: _xmpp-client._tcp.192.168.1.21
(12:05:05) dnssrv: Couldn't look up SRV record. The filename, directory name, or volume label syntax is incorrect. (123).
(12:05:05) dnsquery: Performing DNS lookup for 192.168.1.21
(12:05:05) dnsquery: IP resolved for 192.168.1.21
(12:05:05) proxy: Attempting connection to 192.168.1.21
(12:05:05) proxy: Connecting to 192.168.1.21:5222 with no proxy
(12:05:05) proxy: Connection in progress
(12:05:05) proxy: Connecting to 192.168.1.21:5222.
(12:05:05) proxy: Connected to 192.168.1.21:5222.
(12:05:05) jabber: Sending (example@192.168.1.21): <?xml version='1.0' ?>
(12:05:05) jabber: Sending (example@192.168.1.21): <stream:stream to='192.168.1.21' xmlns='jabber:client' xmlns:stream='http://etherx.jabber.org/streams' version='1.0'>
(12:05:05) jabber: Recv (579): <?xml version='1.0' encoding='UTF-8'?><stream:stream xmlns:stream="http://etherx.jabber.org/streams" xmlns="jabber:client" from="192.168.1.21" id="da08260e" xml:lang="en" version="1.0"><stream:features><starttls xmlns="urn:ietf:params:xml:ns:xmpp-tls"></starttls><mechanisms xmlns="urn:ietf:params:xml:ns:xmpp-sasl"><mechanism>PLAIN</mechanism><mechanism>CRAM-MD5</mechanism><mechanism>DIGEST-MD5</mechanism><mechanism>ANONYMOUS</mechanism></mechanisms><auth xmlns="http://jabber.org/features/iq-auth"/><register xmlns="http://jabber.org/features/iq-register"/></stream:features>
(12:05:05) jabber: Sending (example@192.168.1.21): <starttls xmlns='urn:ietf:params:xml:ns:xmpp-tls'/>
(12:05:05) jabber: Recv (50): <proceed xmlns="urn:ietf:params:xml:ns:xmpp-tls"/>
(12:05:05) nss: SSL version 3.1 using 128-bit AES with 160-bit SHA1 MAC
Server Auth: 2048-bit RSA, Key Exchange: 1024-bit DHE, Compression: NULL
Cipher Suite Name: TLS_DHE_RSA_WITH_AES_128_CBC_SHA
(12:05:05) nss: subject=CN=Unknown,OU=Unknown,O=REDACTED,L=REDACTED,ST=REDACTED,C=US issuer=CN=Unknown,OU=Unknown,O=REDACTED,L=REDACTED,ST=REDACTED,C=US
(12:05:05) certificate/x509/tls_cached: Starting verify for 192.168.1.21
(12:05:05) certificate/x509/tls_cached: Certificate 192.168.1.21 expired at Mon Aug 29 09:54:35 2016
(12:05:05) certificate/x509/tls_cached: Checking for cached cert...
(12:05:05) certificate/x509/tls_cached: ...Found cached cert
(12:05:05) nss/x509: Loading certificate from C:UsersexampleAppDataRoaming.purplecertificatesx509tls_peers2.168.1.21
(12:05:05) certificate/x509/tls_cached: Peer cert matched cached
(12:05:07) util: Writing file accounts.xml to directory C:UsersexampleAppDataRoaming.purple
(12:05:07) util: Writing file C:UsersexampleAppDataRoaming.purpleaccounts.xml
(12:05:07) util: Writing file blist.xml to directory C:UsersexampleAppDataRoaming.purple
(12:05:07) util: Writing file C:UsersexampleAppDataRoaming.purpleblist.xml
(12:05:07) certificate/x509/tls_cached: User ACCEPTED cert
Caching first in chain for future use as 192.168.1.21...
(12:05:07) nss/x509: Exporting certificate to C:UsersexampleAppDataRoaming.purplecertificatesx509tls_peers2.168.1.21
(12:05:07) util: Writing file C:UsersexampleAppDataRoaming.purplecertificatesx509tls_peers2.168.1.21
(12:05:07) nss: Trusting CN=Unknown,OU=Unknown,O=REDACTED,L=REDACTED,ST=REDACTED,C=US
(12:05:07) certificate: Successfully verified certificate for 192.168.1.21
 Komp
Komp